Settings And Users
API Keys
How to create, manage, and revoke API keys for programmatic access to Hygiara.
What this page is for
This page explains how to create and manage API keys so you can authenticate against the Hygiara REST API from scripts, pipelines, or other tools.
When to use it
Use API keys when:
- you want to trigger reviews from a CI/CD pipeline
- you are building scripts that query review results or download reports
- you need a service account style access path that does not depend on a user session
How to create an API key
- Go to Settings.
- Click the API Keys tab.
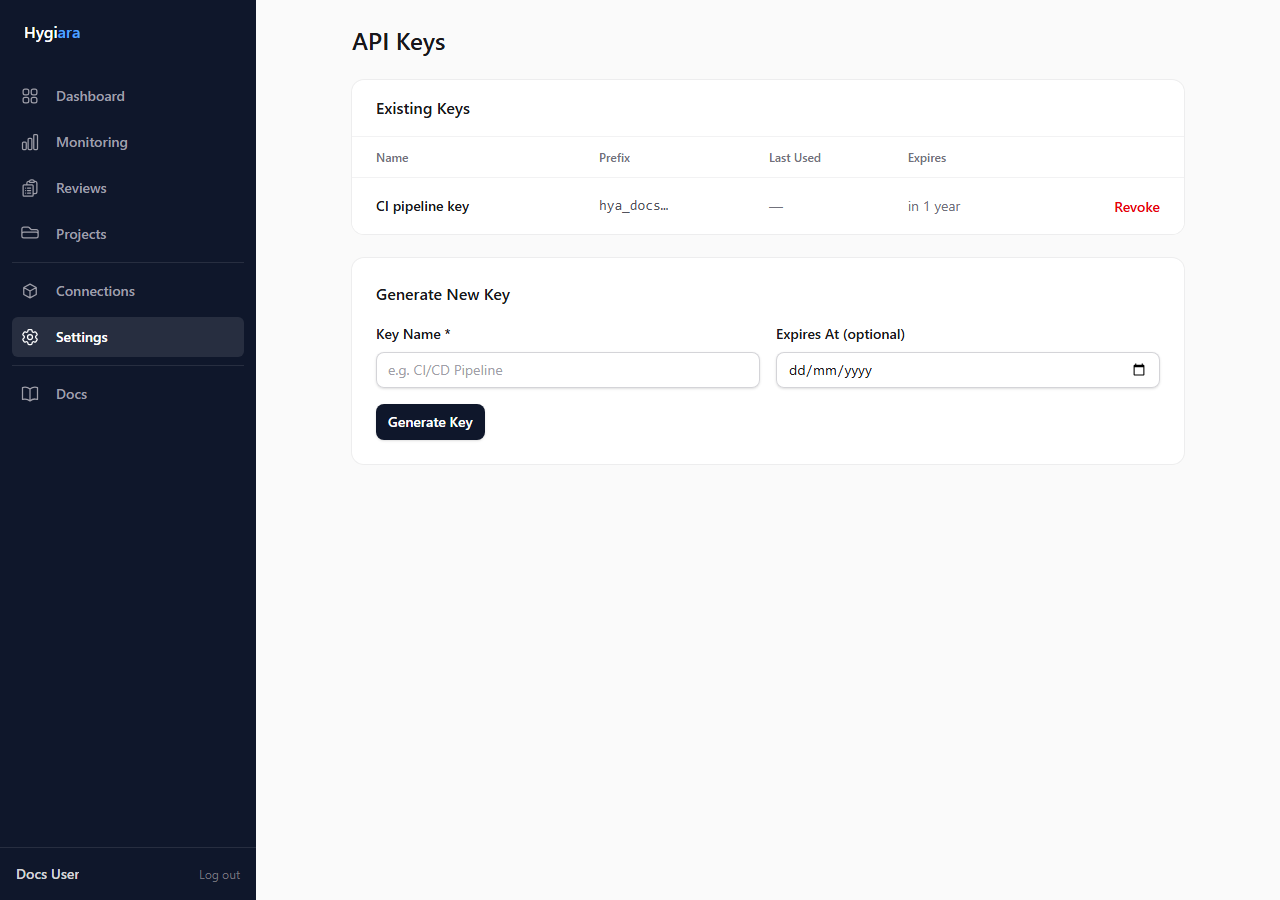
- Click Create API Key.
- Give it a name that identifies its purpose (for example: "CI pipeline" or "Reporting script").
- Optionally set an expiry date.
- Click Create.
Important: The full API key value is only shown once, immediately after creation. Copy it and store it securely. You will not be able to retrieve it again.
Key format
API keys are prefixed with hrdly_ so they are easy to identify if they appear in logs or config.
How to use an API key
Include the key in the X-API-Key header of your API requests:
X-API-Key: hrdly_your_key_value_here
For exact endpoint details, use the generated API reference.
Managing existing keys
From the API Keys tab you can see:
- the key name
- the key prefix (for identification)
- the last time the key was used
- the expiry date (if set)
- whether the key is expired
Use the actions menu to revoke a key immediately. Revoked keys cannot be used and cannot be reinstated.
What to expect
A revoked key stops working immediately. There is no grace period.
If you lose a key, revoke the old one and create a new one.
Common mistakes
- Not setting an expiry date on keys used in temporary scripts — revoke them manually when the work is done
- Sharing a single key between multiple pipelines — use one key per pipeline so you can revoke them independently
- Storing keys in source control (use environment variables or a secrets manager instead)